Get In Touch
We’d love to hear from you! Whether you have a question, need support, or just want to share your feedback,
Our team is here to help. We look forward to connecting with you!
Download the Cybersecurity Two-pager.
A clear overview you can use to package cybersecurity into your proposals.

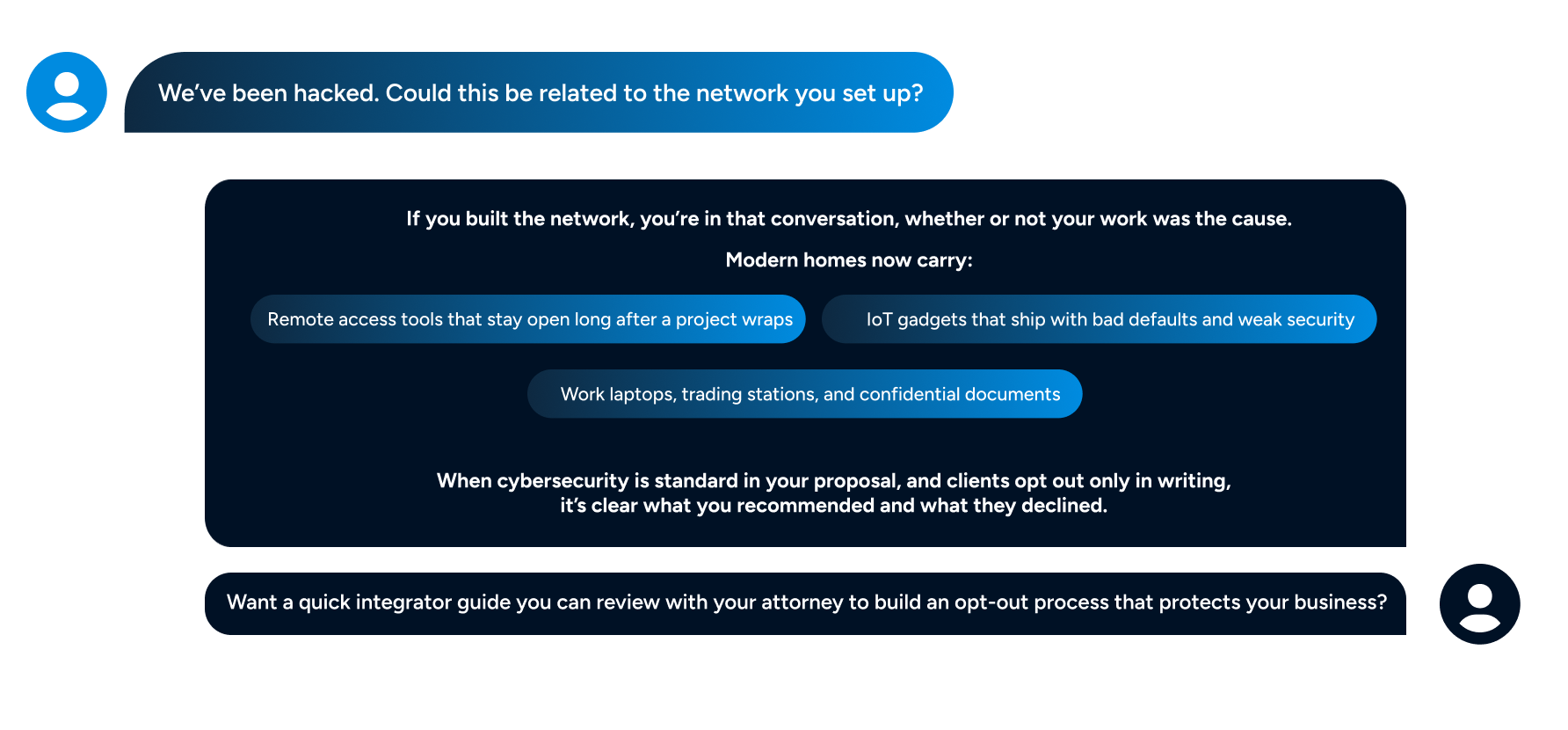
Reduce liability when any client network you touch gets pulled into a breach








(1Password)
(Up to 3 PCs and 3 mobile devices)



Dark web monitoring
(Up to 3 users)





































Blocks attacks on
computers in real time
(Falcon endpoint protection / EDR)
(Up to 3 PCs and 3 mobile devices)

Dark web monitoring
(Up to 3 users)

Dark web monitoring
(Up to 3 users)
AI-driven threat intelligence with Cisco Talos
Threat detection and filtering with protection against:
Intrusion Detection System and Intrusion Prevention System
(IDS + IPS)



The home was located in a gated community with a professionally installed smart home system, including surveillance, access control, and a managed Wi-Fi network.
The home was located in a gated community with a professionally installed smart home system, including surveillance, access control, and a managed Wi-Fi network. The wireless network name included the family’s last name, making it identifiable from outside the property.
An individual walking through the neighborhood located the network and began testing login credentials obtained from a previous third-party data breach. One device on the network had not received recent firmware updates, which allowed access beyond the initial connection point.
Once inside the network, the attacker accessed email accounts used by the household. Over several days, he reviewed communication patterns between the family, their staff, and outside vendors. Messages were then sent that appeared consistent with prior conversations, including revised payment instructions tied to an active transaction.
Funds were transferred based on those instructions before the activity was flagged as fraudulent. Law enforcement was contacted after the transfers were completed. A portion of the funds was recovered, but a significant amount was not.
The access point into the network was a combination of reused credentials and an unpatched device.

A residential property had a network-connected pool control system, including a Jandy controller, integrated into the same network used by personal devices and computers.
A residential property had a network-connected pool control system, including a Jandy controller, integrated into the same network used by personal devices and computers.
The controller had a known vulnerability that had been addressed by the manufacturer in a firmware update. However, the update had not been applied.
An attacker identified the exposed vulnerability and used it to gain access to the home network through the pool control system. Because the device was connected to the primary network, the attacker was able to move laterally and reach other devices, including personal computers.
From there, sensitive information was accessed, including stored credentials and financial data. The attacker later used this information to access banking accounts and transfer funds.
The homeowner was not aware of the vulnerability or the need to update the pool controller firmware. The compromise originated from a non-traditional device that was treated as part of the home system rather than as a potential network entry point.
Cyber risk is no longer unusual. Nearly three in four Americans say they have already been hit by an online scam or attack.
The financial fallout is real: consumers reported over $12.5 billion in fraud losses in 2024.
Internet crime is hitting at scale, with the FBI logging nearly 860,000 complaints and more than $16 billion in losses last year.
Many breaches still start the same way: stolen logins and vulnerabilities that were left exposed.
We’d love to hear from you! Whether you have a question, need support, or just want to share your feedback,
Our team is here to help. We look forward to connecting with you!